At a Glance
- Dwell time: 2 days
- Initial access: RDP brute force (targeted wordlist)
- Defense evasion: privacy.sexy
- C2: Cobalt Strike + custom TCP beacon
- Lateral movement: RDP and SMB
- Exfiltration: Custom exfil tool, 6,900+ unique Cloudflare IPs over 443
- Extortion: Personalized note for each user, 2 templates (leadership / employee)
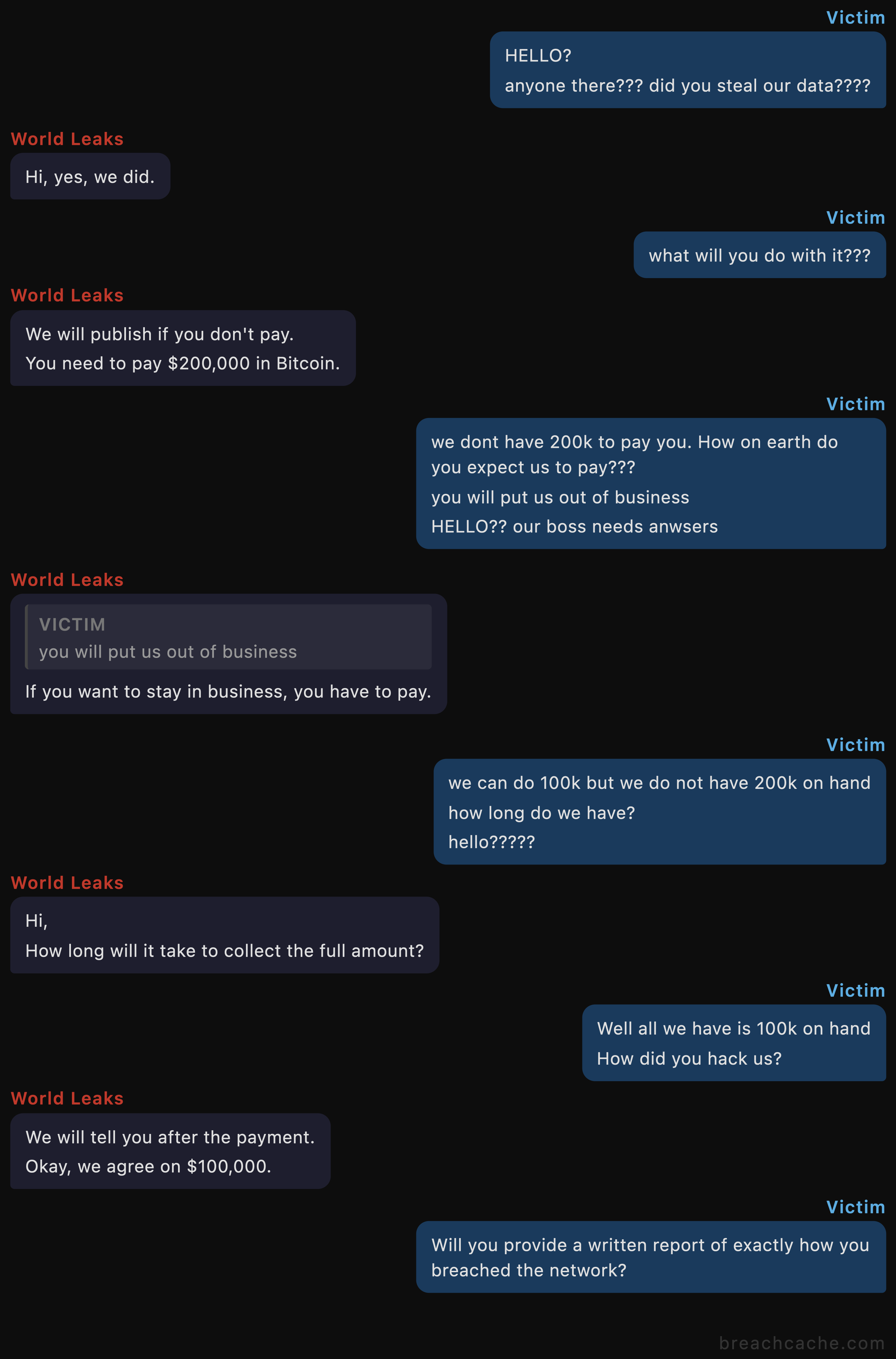
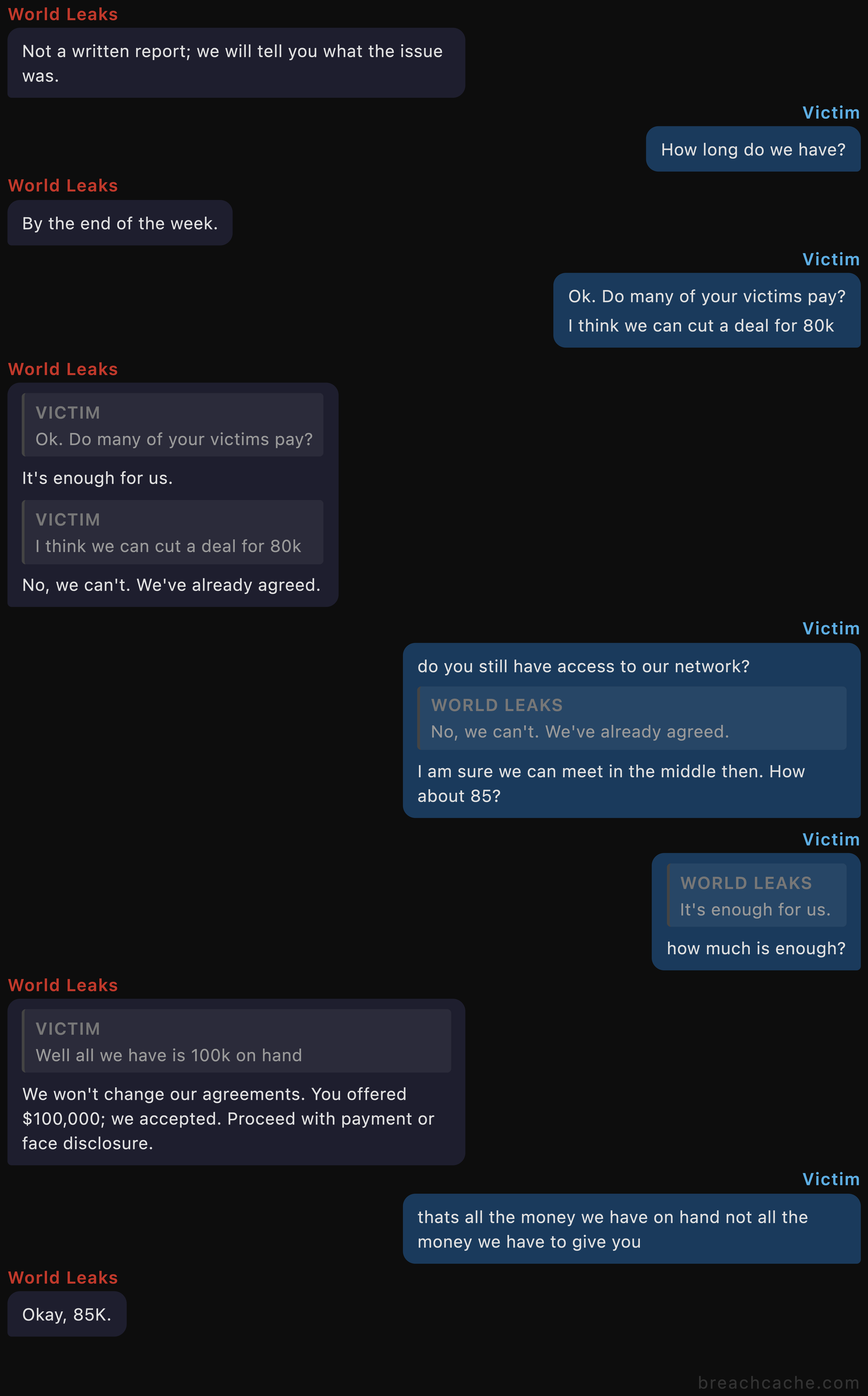
- Negotiation: $200,000 BTC demanded, negotiated down to $85,000, full negotiation chats included
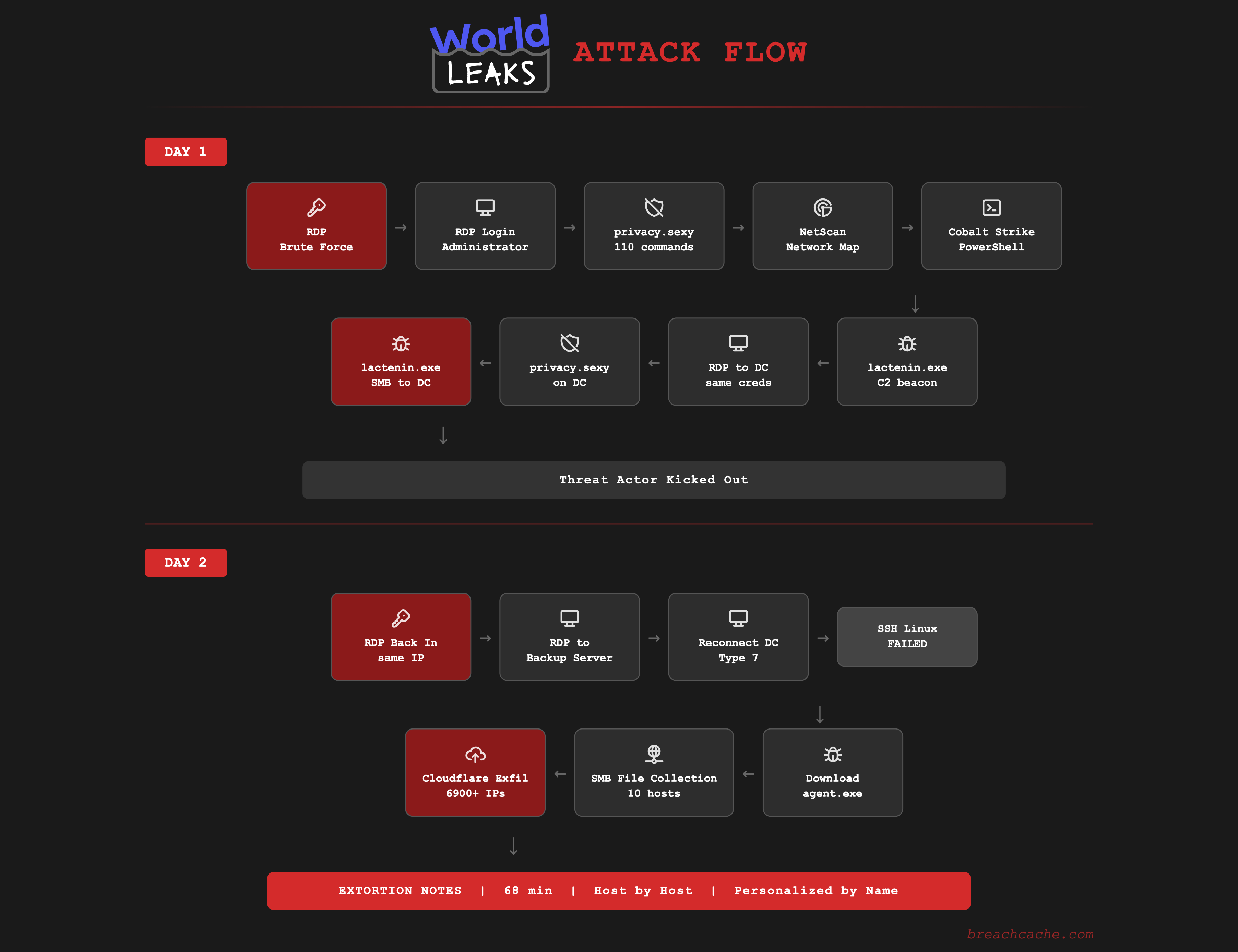
Executive Summary
Over this two day intrusion World Leaks gained initial access to the network and quickly moved to critical infrastructure including the domain controller and backup server. The threat actor’s goal was to access and exfiltrate sensitive corporate data across the organization which they used to pressure the victim into paying an extortion demand.
The threat actor brute forced the Administrator account on an exposed RDP service using a targeted wordlist specific to the company. The password would not have been found on a common wordlist indicating the threat actor performed reconnaissance on the organization prior to the brute force. Within 2 minutes of logging in the threat actor executed privacy.sexy to disable security controls and then deployed SoftPerfect Network Scanner with a pre built config to map the network. They then deployed a Cobalt Strike stager directly into PowerShell process memory and dropped lactenin.exe which is malware masquerading as a Microsoft Edge Update installer.
The threat actor moved laterally to the domain controller over RDP using the same Administrator credentials and replicated their tools across. They ran the same privacy.sexy script on the domain controller and copied lactenin.exe over SMB executing it immediately. The threat actor was removed from the network the same day.
The threat actor regained access the following day due to the original RDP exposure not being remediated. They accessed the backup server within 2 minutes of regaining access and attempted SSH connections to the Linux file server which all failed. The threat actor then downloaded agent.exe (RustyRocket, first identified and named by Accenture) which is a custom exfiltration platform that World Leaks distributes to their operators. An operator README that was able to be recovered indicates this is a maintained platform with three operating modes, persistence recipes, and a companion pivoting proxy for segmented networks.
Both the domain controller and backup server ran agent.exe simultaneously connecting to over 6,900 unique Cloudflare IPs over 443 to exfiltrate data collected over 445 from every reachable host. After exfiltrating the data the threat actor spent 68 minutes placing personalized extortion notes on every reachable workstation addressed by name to each user with separate templates for leadership and employees.
Initial Access
The threat actor first probed the exposed RDP service the day before with 2 SYN packets from 45.227.254[.]128 at 05:53 UTC. On Day 1 the first failed authentication attempt (Event 4625) was observed at 11:05 UTC and the brute force succeeded 2 minutes later at 11:07 UTC which was observed as a Type 3 NLA validation event with workstation name SBSSRV. The threat actor manually logged in over RDP 4 minutes later at 11:11 UTC. The password was custom to the organization and would not have been found on a common wordlist. This indicates the threat actor performed reconnaissance on the company prior to the brute force and built a targeted wordlist incorporating the company name.
The source IP 45.227.254[.]128 is a Windows Server 2012 R2 machine (hostname SBSSRV) hosted by Flyservers/XWIN UNIVERSAL (AS267784). This same IP was used across both phases of the intrusion with external RDP authentications Day 1 and Day 2 after the threat actor was kicked out. The RDP exposure was not remediated. The threat actor regained access the following day from the same source IP.
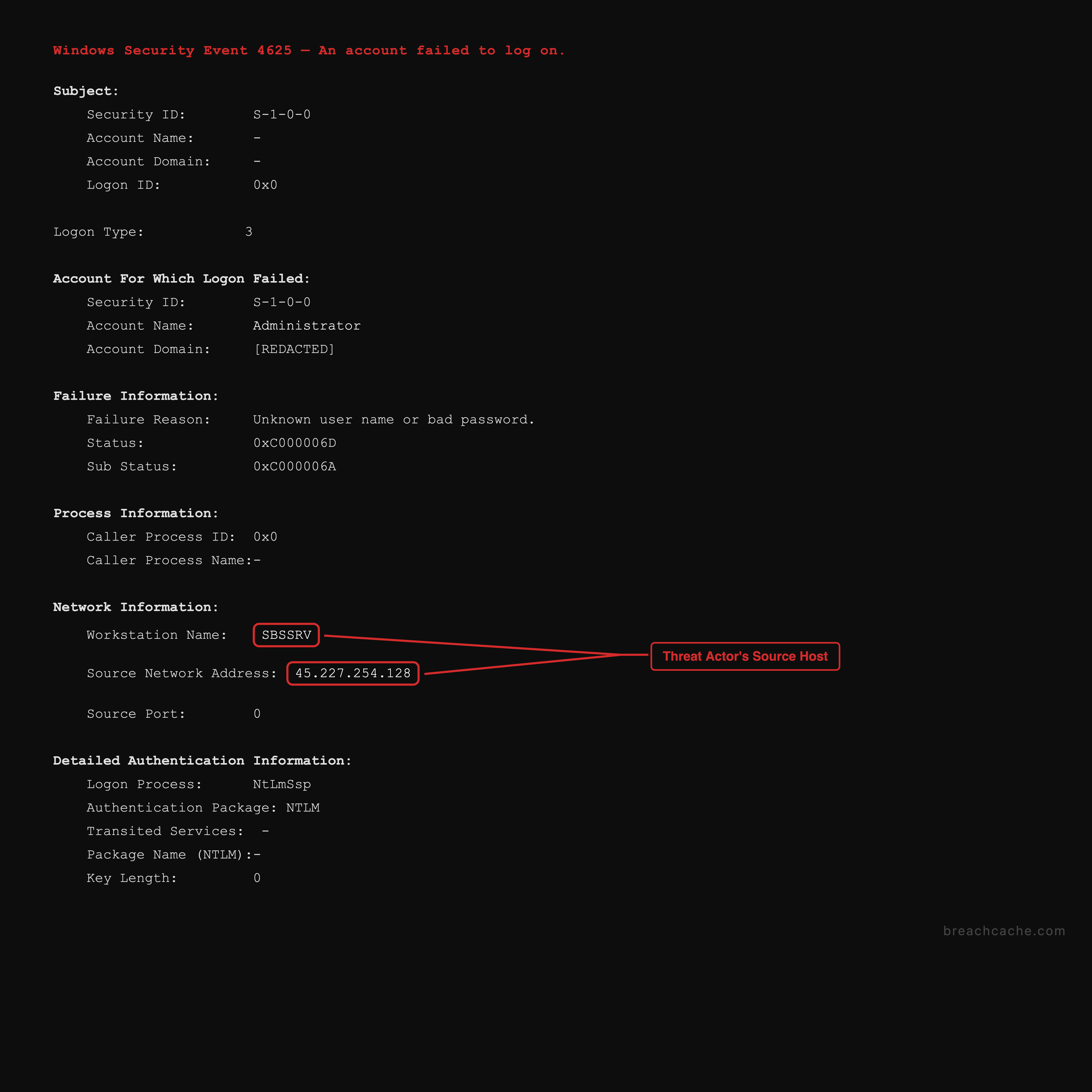
Reconnaissance:
Day before, 05:53:47 UTC 2 SYN packets from 45.227.254[.]128 (probe)
Brute Force:
Day 1, 11:05:01 UTC First failed logon (Event 4625, Administrator)
Day 1, 11:07:12 UTC Brute force succeeds (Type 3, workstation: SBSSRV)
2,153 failed logon attempts (Event 4625) from SBSSRV
RDP Logon:
Time: 11:11:38 UTC (4 minutes after brute force success)
Source: 45.227.254[.]128 (Flyservers/XWIN UNIVERSAL, Vilnius LT, AS267784)
Target: Entry workstation, port 3389
Account: Administrator
Logon Type: 10 (RemoteInteractive)
Day 2 Regained access:
Source: 45.227.254[.]128 (same IP)
Account: AdministratorEstablishing a Foothold
privacy.sexy
The threat actor used scripts generated by privacy.sexy which is a legitimate open source privacy hardening tool that can be found online.
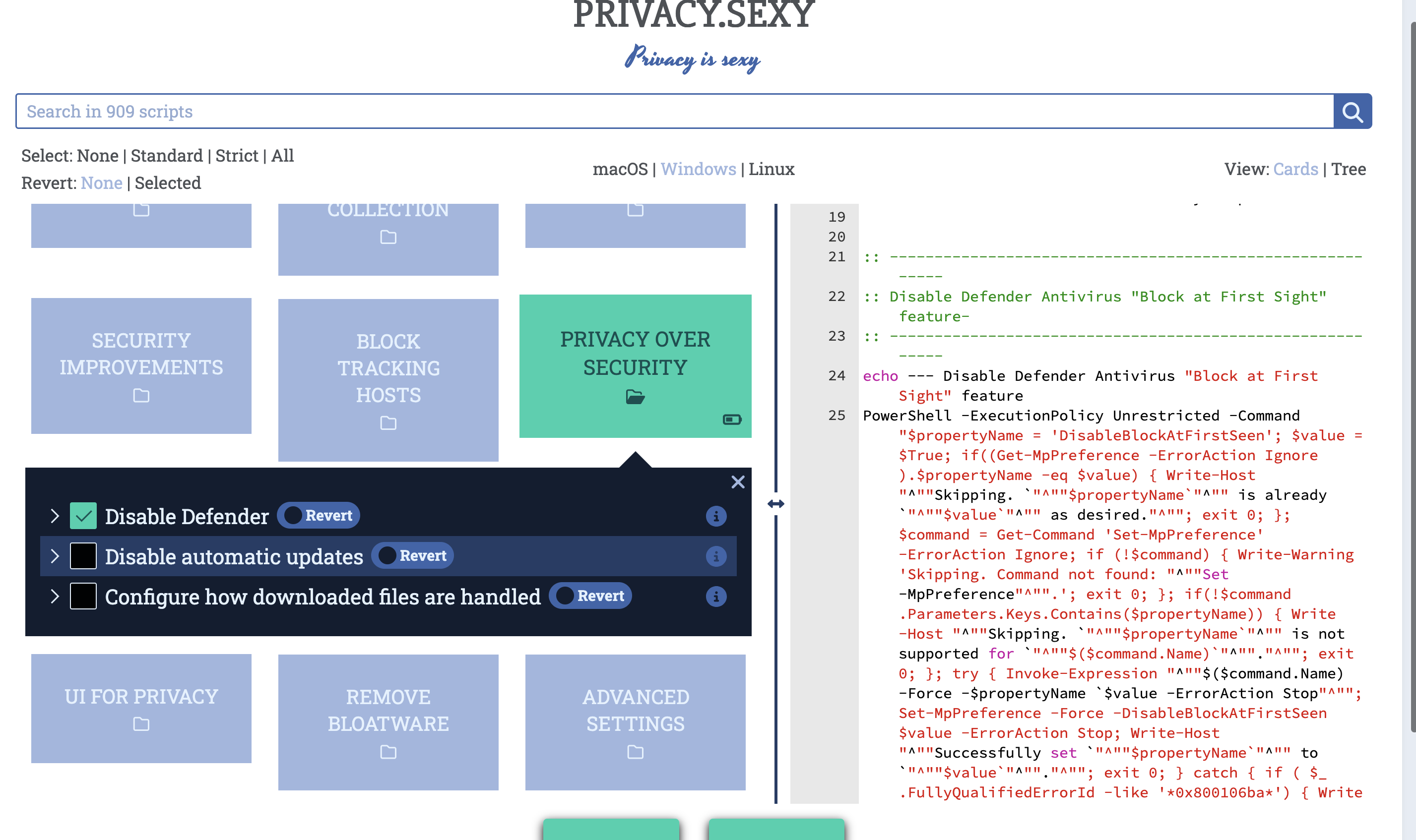
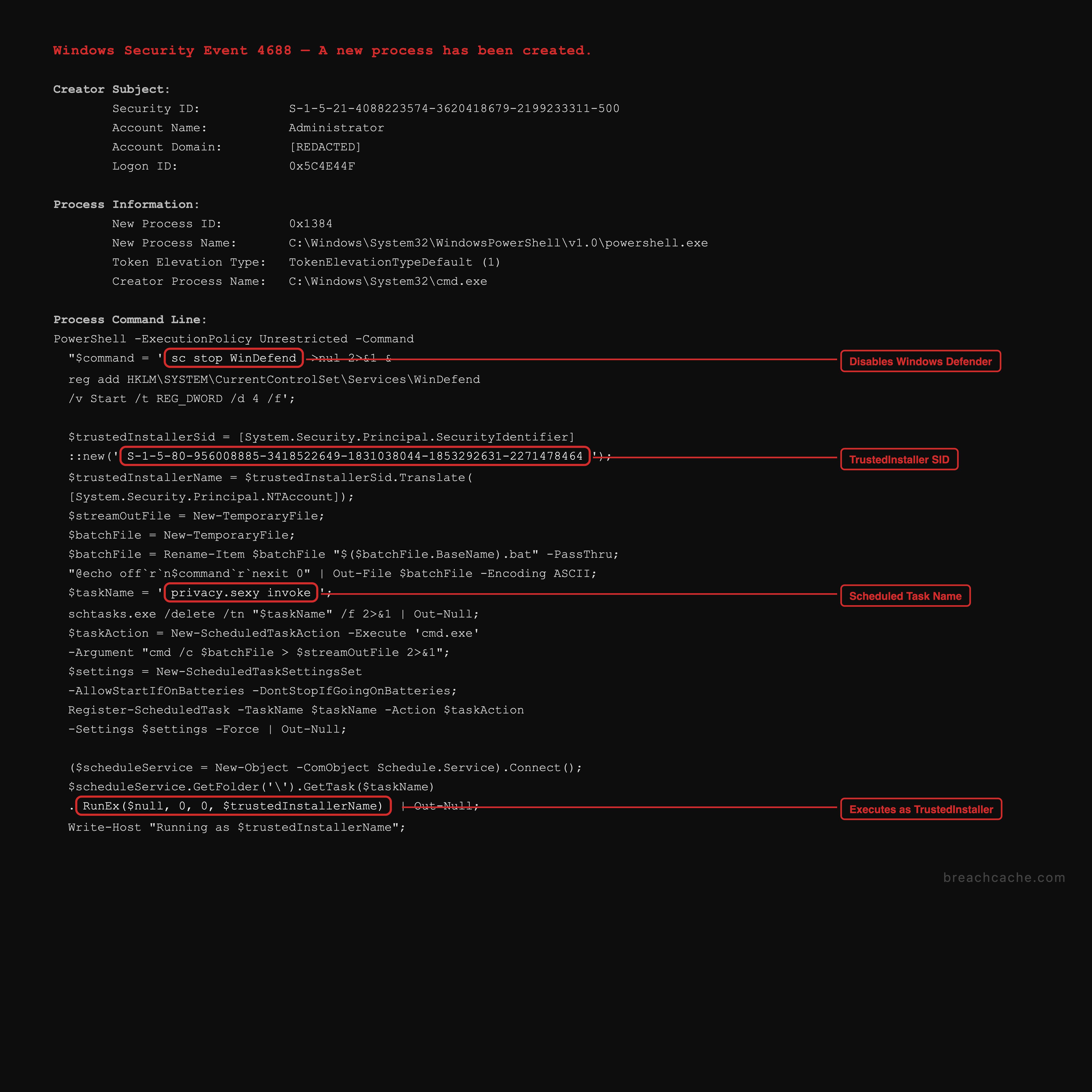
The script uses a TrustedInstaller privilege escalation to execute commands that even local administrators cannot run directly. It works by creating a scheduled task named privacy.sexy invoke and then using the Schedule.Service COM object to call RunEx() on that task passing in the TrustedInstaller SID (S-1-5-80-956008885-3418522649-1831038044-1853292631-2271478464) as the execution identity. Because TrustedInstaller is the owner of protected system services like WinDefend the task runs with the permissions needed to stop and disable them. The script wraps the actual commands in a temporary batch file which gets executed through cmd.exe under the TrustedInstaller context.
The threat actor executed the script on the entry workstation at 11:13 UTC. The script executed 110 commands in 8 seconds disabling WinDefend, MpsSvc, Sense, WdNisSvc and SecurityHealthService. This tool has previously been observed used by Octo Tempest, a BlackCat/ALPHV affiliate, as documented by Microsoft in October 2023.
SoftPerfect Network Scanner (netscan.exe)
The threat actor deployed SoftPerfect Network Scanner (netscan.exe) on the entry workstation at 11:17 UTC. The tool was copied from the threat actor’s server and extracted from a zip file via Windows Explorer. This was a licensed copy which includes additional features over the free version and it came with a pre built configuration file. The config had TCP port scanning enabled for 22, 389, 443, 445, 636, 902, 3389, 2179, 5000, 5001, 6170, 8080, 9401 and 9091. Port 9401 is the Veeam Backup Service secure connection port which is used by the mount server to communicate with the backup server. The inclusion of this port in the scan config suggests the threat actor routinely targets Veeam backup infrastructure. Share enumeration was enabled with write access checking turned on which allowed the threat actor to identify which shares they could write to across the network. The config also had workstation enumeration enabled for user accounts, disk drives, LAN groups, logged in users, roles and uptime. The tool ran on Day 1 from 11:17 to 11:39 UTC scanning 14 unique hosts across the network and was used again on Day 2 from 05:58 to 08:35 UTC to access SMB shares for placing the extortion notes.
Config highlights:
TCP ports: 22, 389, 443, 445, 636, 902, 3389, 2179, 5000, 5001, 6170, 8080, 9401, 9091
Share enumeration: enabled
Write access check: enabled
Share security info: enabled
Disk space check: enabled
Workstation enumeration: accounts, disk drives, LAN group, logged users, roles, uptime
Max threads: 50
Randomized scan order: enabled
Day 1: 11:17 to 11:39 UTC (network mapping, 255 events, 14 hosts)
Day 2: 05:58 to 08:35 UTC (SMB access for extortion notes, 502 events, 13 hosts)Cobalt Strike
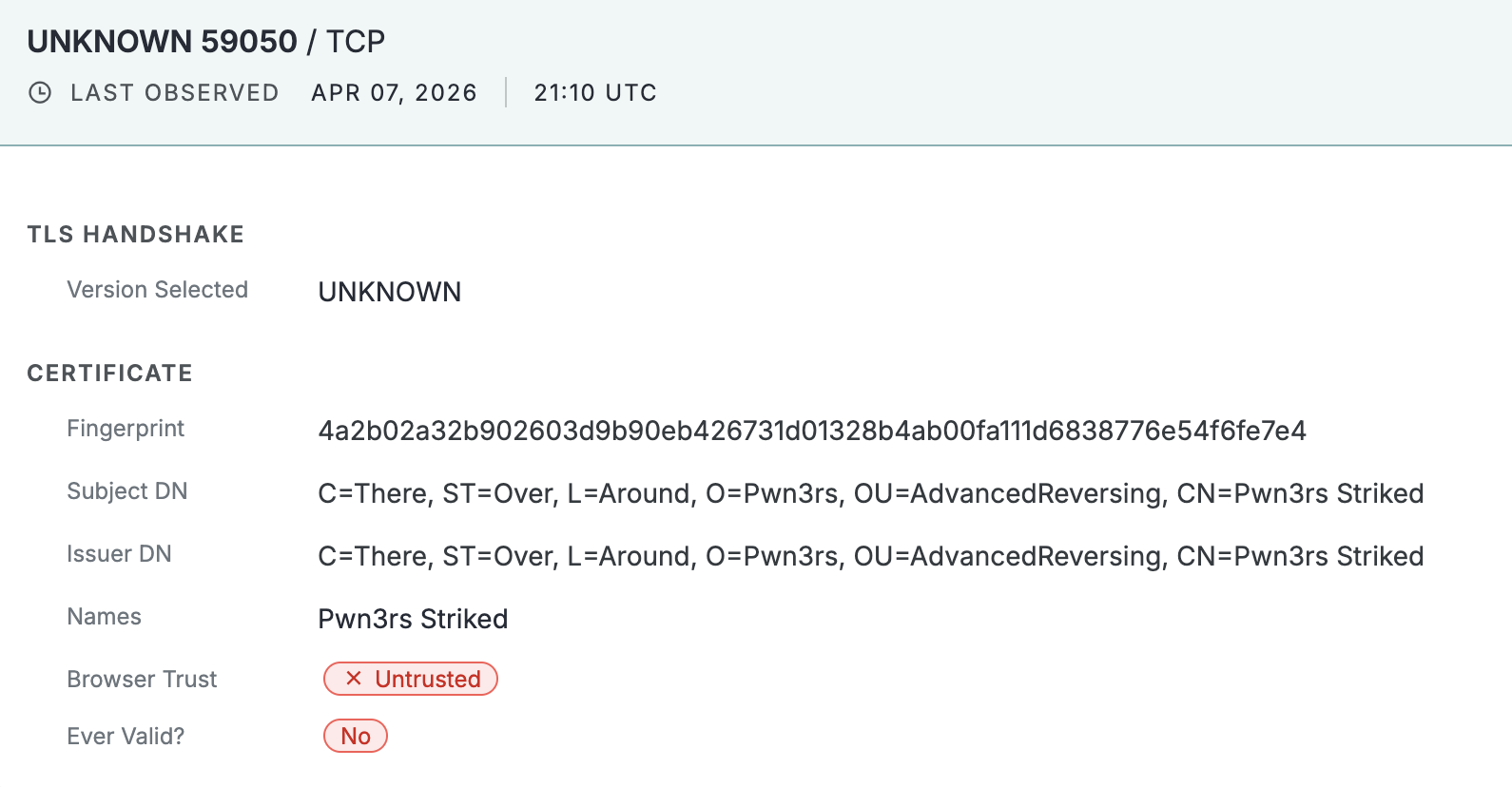
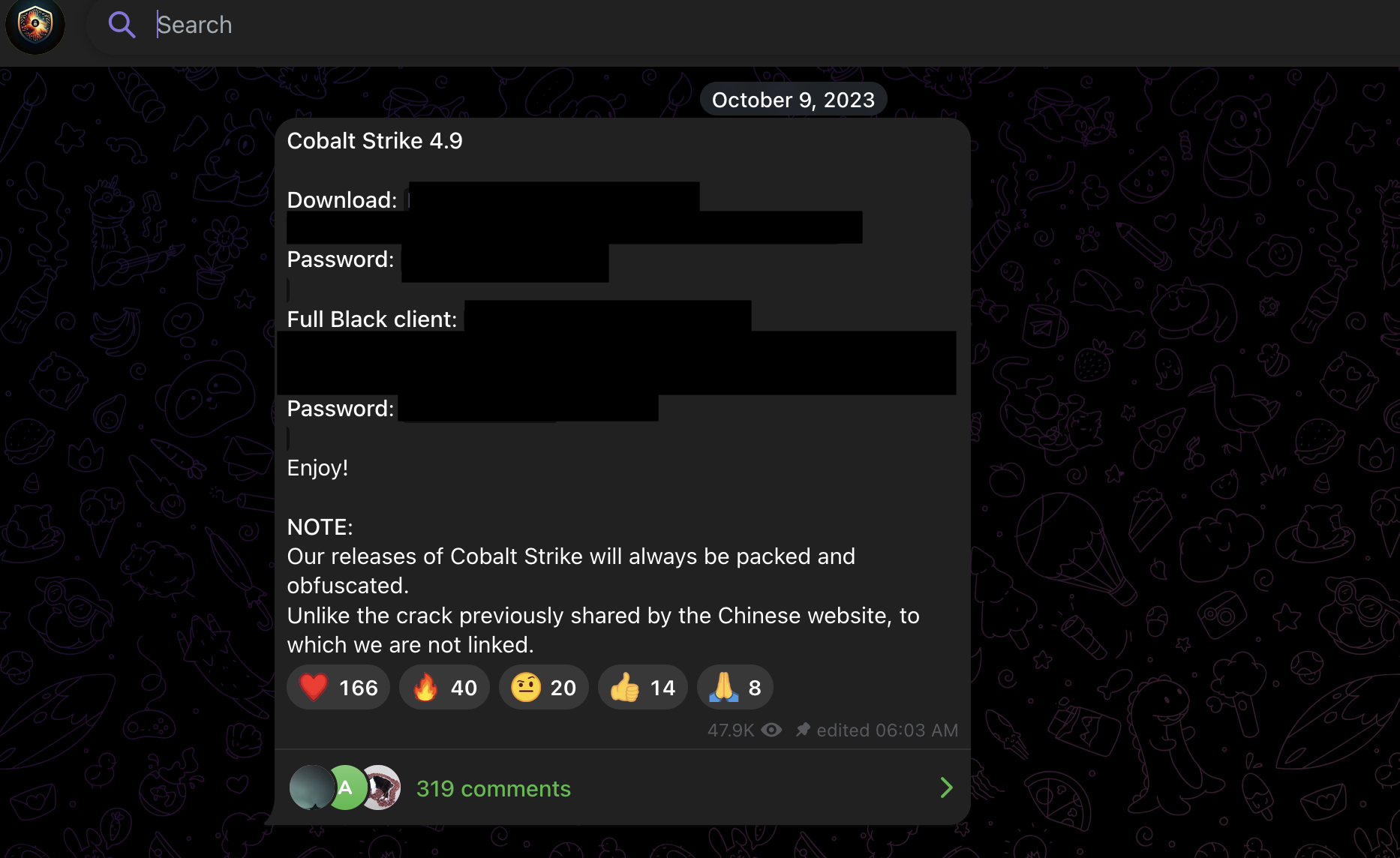
At 11:26 UTC a Cobalt Strike PowerShell stager was deployed manually by the threat actor copying and pasting into the PowerShell terminal. The command decoded base64 which then unzipped a blob leading to shell code injection into the PowerShell process. The beacon communicated with 45.227.253[.]139 over 31822 using the URI /8qiJ. The same IP was observed hosting a TLS service on port 59050 with a self signed certificate issued to CN=Pwn3rs Striked (O=Pwn3rs, OU=AdvancedReversing) which is associated with a cracked version of Cobalt Strike distributed through a popular software cracking Telegram channel Pwn3rs.
lactenin.exe
The threat actor deployed lactenin.exe which is a malware masquerading as a Microsoft Edge Update installer to the C:\inetpub\ directory on the entry workstation. The binary is written in Go and obfuscated using a science fiction theme for its variable and function names including turretController, navigationData, optimizeTargetingAlgorithm, manageCoolingSystem, powerDistributor, threatAssessment, and Plasma Conduit Calibration. The binary uses a self signed certificate (C2RService, untrusted root) and contained metadata referencing Microsoft Corporation with the original filename MicrosoftEdgeUpdateSetup.exe. The tool was downloaded from temp[.]sh. lactenin.exe beaconed to 195.66.213[.]218 over 4381.
File: C:\inetpub\lactenin.exe
SHA256: a80f5c877ccc7fa71b9de1eb9bd82f9525f1ab282d15c4b4beaffabbf3064c31
Language: Go based
Masquerade: MicrosoftEdgeUpdateSetup.exe
Download: temp[.]sh
C2: 195.66.213[.]218:4381 (3-4 minute beacon intervals)
Certificate: Self signed (C2RService, untrusted root)
Execution on entry workstation:
Time: Day 1, 11:31:06 UTC | PID: 5784 | Parent: Explorer.EXELateral Movement
The threat actor moved laterally to the domain controller over RDP at 11:31 UTC using the same Administrator credentials they brute forced. They ran the same privacy.sexy script on the domain controller at 11:32 UTC disabling the same security controls. They then copied lactenin.exe from the entry workstation to the domain controller over SMB at 11:38 UTC and executed it immediately. The file was written over SMB using SoftPerfect Network Scanner sourcing from the entry workstation. The threat actor also attempted to download PSTools from Microsoft’s official site via Chrome on the domain controller but was removed from the network before the download completed.
Day 1:
11:11:38 UTC RDP into entry workstation (initial access from 45.227.254[.]128)
11:31:48 UTC RDP to domain controller (same brute forced Administrator account)
11:32:32 UTC `privacy.sexy` executed on domain controller
11:38:30 UTC lactenin.exe copied to DC over SMB
11:38:44 UTC lactenin.exe executed on DCOn Day 2 the threat actor logged back into the entry workstation at 05:57 UTC from 45.227.254[.]128. 2 minutes later they were on the backup server at 05:59 UTC which was the first host they moved to after regaining access. Seconds after logging in the threat actor launched the Veeam Backup and Replication console (veeam.backup.shell.exe) and began browsing through backup jobs, repositories, and storage configurations. The threat actor spent roughly 3 minutes inside the Veeam console looking for indications of virtualized infrastructure being backed up including VMware vSphere, Hyper-V, and Proxmox workloads. During the same window the threat actor pinged 45.227.254[.]128 and 45.227.253[.]139 from the backup server to confirm outbound reachability to their operating server and Cobalt Strike C2 before deploying additional tools. This was consistent with the NetScan config deployed on Day 1 which had port 9401 (Veeam Backup Service) enabled in its scan list indicating the threat actor routinely targets backup infrastructure as part of their operations.
At 06:23 UTC the threat actor ran mstsc.exe targeting the domain controller IP on the entry workstation. The logon on the domain controller was recorded as a Type 7 (Unlock/Reconnect) not a Type 10 which means the RDP session from Day 1 was still active on the domain controller and the threat actor reconnected to it rather than starting a new session.
Domain Controller Reconnect:
06:23:53 UTC mstsc.exe /v:[DC IP] on entry workstation
06:24:07 UTC Type 7 logon on domain controller
Account: Administrator
Source: [Entry workstation IP]
Auth Package: Negotiate
Elevated Token: Yes
Note: Type 7 = session reconnect, not new sessionThe threat actor attempted SSH connections from the domain controller to the Linux file server using lactenin.exe over 22 trying a backup service account and then root but all 4 attempts failed.
Day 2:
05:57:54 UTC RDP back into entry workstation (regained access from 45.227.254[.]128)
05:59:09 UTC RDP to backup server (Administrator)
06:06:35 UTC ping 45.227.254[.]128 from backup server
06:06:56 UTC ping 45.227.253[.]139 from backup server
06:23:53 UTC RDP reconnect to domain controller (Type 7, Day 1 session still active)
06:42:41 UTC SSH to file server via lactenin.exe (failed)
06:43:11 UTC SSH failed: backup service account
06:43:28 UTC SSH failed: backup service account
06:52:18 UTC SSH failed: root
06:52:32 UTC SSH failed: root
06:53:55 UTC RDP to backup server (backup service account)
07:01:04 UTC RDP to workstation 1 (owner account)
08:57:09 UTC RDP to domain controller (domain admin account)Recorded footage from day 2 of the intrusion:
Exfiltration
RustyRocket (agent.exe)
After the failed SSH attempts the threat actor opened Chrome on the domain controller and downloaded agent.zip from temp[.]sh at 06:45 UTC.
![agent.zip downloaded from temp[.]sh](/cases/worldleaks-extortion/tempsh-agent.png)
The threat actor extracted agent.exe and placed it in C:\ProgramData\Veeam\ on the domain controller. This path did not exist on the domain controller and was created by the threat actor to mimic legitimate Veeam infrastructure. 8 minutes later the threat actor copied agent.exe over SMB to the backup server where C:\ProgramData\Veeam\ was a legitimate path used by the Veeam Backup and Replication installation. An operator README titled Documentation that was able to be recovered indicates this is a maintained exfiltration platform that World Leaks distributes to their operators.
File: C:\ProgramData\Veeam\agent.exe
SHA256: 743f9dbb32f86322c5f55f1e9051c5cd88092f10adcdac45aa648ac06e229b8a
Language: Rust
Download: temp[.]sh
Companion: Pivoting Proxy (not observed in this intrusion)The help output from agent.exe reveals the full command line interface available to operators:
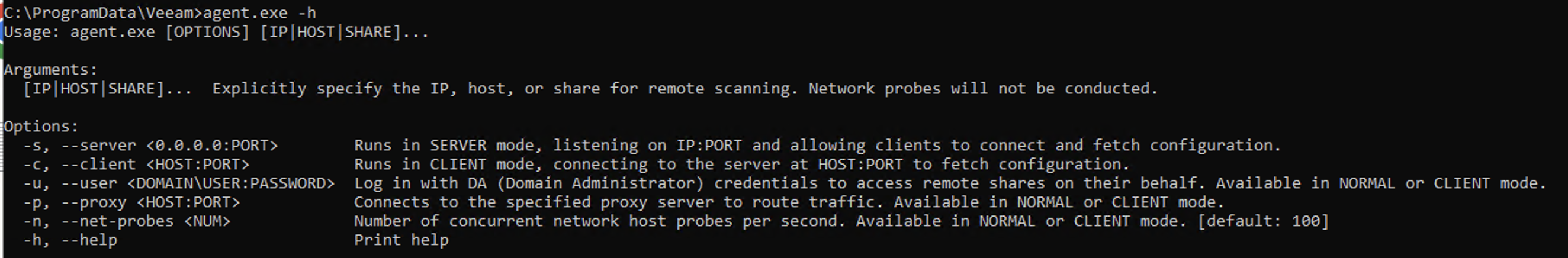
The tool accepts IP addresses, hostnames, or share paths as arguments for targeted scanning. The —server and —client flags enable the distributed CLIENT/SERVER mode where one instance serves configuration to others across the network. The —user flag accepts domain administrator credentials in DOMAIN\USER:PASSWORD format to authenticate against remote shares. The —proxy flag connects to the companion pivoting proxy for routing traffic out of segmented networks. The —net-probes flag controls the number of concurrent host probes per second which defaults to 100.
Notable Snippets From Operator README
From the recovered documentation:
‘The Agent Software is designed to index files across the network and securely transfer them to Secure Cloud Storage. It is essential to manage the encrypted configuration carefully to prevent interception.’
Operating Modes:
NORMAL: Reads encrypted config from stdin. Indexes files. Transfers to cloud.
CLIENT/SERVER: Multiple clients across network with one server. Can run as SYSTEM.
SERVER (Linux): Listens for client connections. Distributes config.
NORMAL mode warning from README:
'Tightly coupled to a user session; if the session is terminated,
the program will stop.'
Documented persistence methods:
1. sc create (local service as SYSTEM via svcrun.exe wrapper)
2. sc \\<RemoteHost> create (remote service deployment)
3. schtasks /create /ru SYSTEM (scheduled task)
Companion tool:
'The Pivoting Proxy Software is useful when a file server is not connected
to the Internet but is accessible from the local network.'The Pivoting Proxy was not observed in this intrusion but its existence in the documentation is notable. The concept is similar to how Cobalt Strike handles segmented networks using SMB beacons that chain through a parent HTTP beacon to reach the internet. In that model a beacon on a host with no internet access communicates over SMB to a beacon on a host that does and the traffic is relayed out. The World Leaks pivoting proxy serves the same purpose for their exfiltration tool. If agent.exe is running on a file server that cannot reach the internet the proxy runs on a host that can and routes the exfiltration traffic through it. The fact that this is a separate documented tool rather than a built in feature suggests World Leaks has encountered enough segmented networks to justify developing a standalone solution for it. As mentioned earlier the threat actor pinged their external infrastructure from the backup server confirming it had internet access. This may have been a test to see if the companion tool was needed.
Deployment
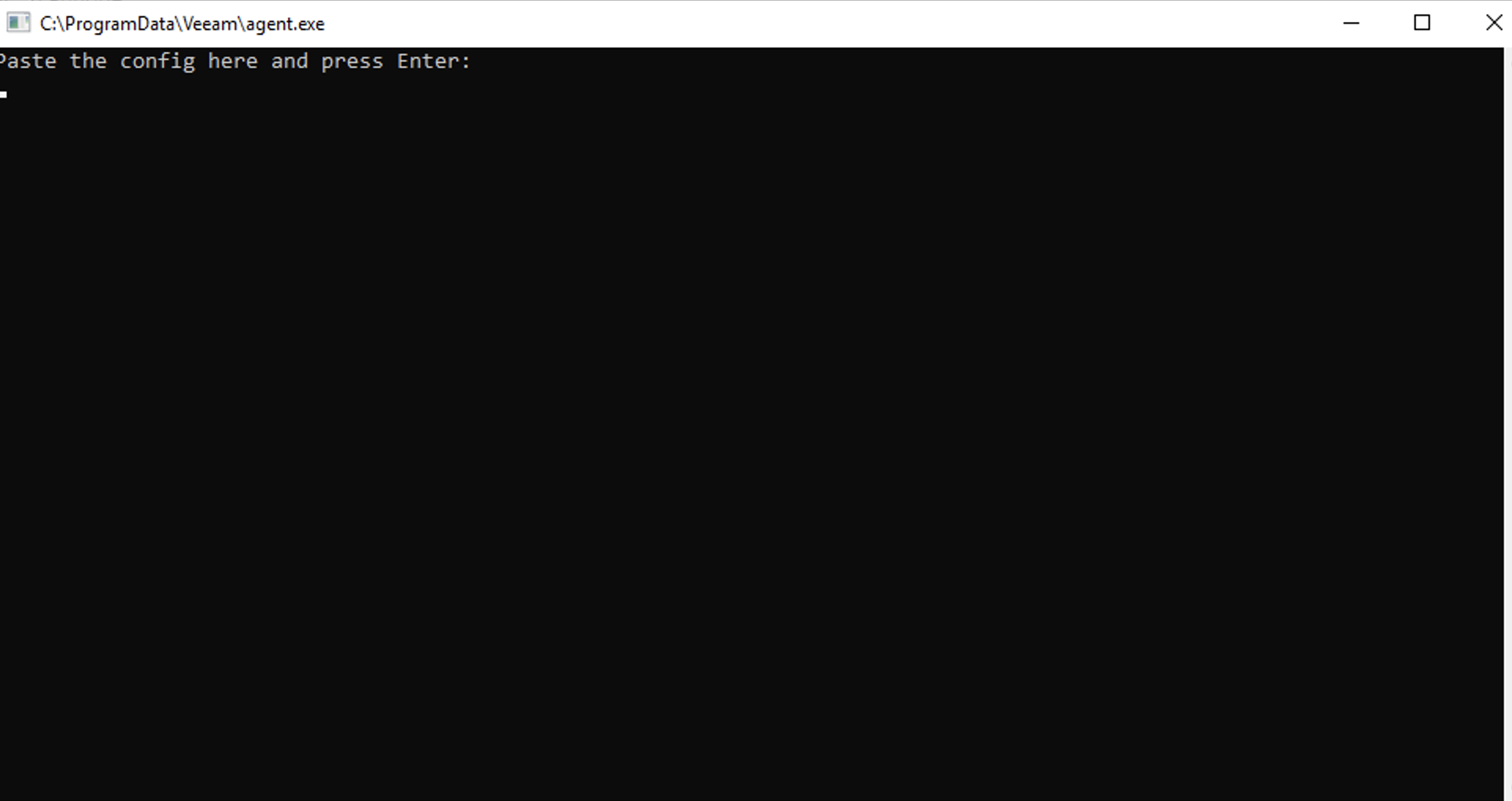
Both instances were executed in NORMAL mode with the encrypted configuration passed manually by the threat actor at run time resulting in agent.exe being ran with no command flags. When executed agent.exe prompts the operator to paste the encrypted configuration directly into the terminal window.
Domain Controller (C:\ProgramData\Veeam\ path created by threat actor):
06:45:30 UTC Chrome opened, agent.zip downloaded from temp[.]sh
06:47:07 UTC agent.exe dropped
06:48:41 UTC Execution
06:49:29 UTC First outbound HTTPS 443 to Cloudflare
Backup Server (C:\ProgramData\Veeam\ legitimate path, Veeam installed):
06:55:30 UTC agent.exe copied over SMB
06:57:37 UTC First outbound HTTPS 443 to CloudflareSMB Collection
The domain controller instance handled the SMB collection connecting to every reachable host across the network over 445 indexing and exfiltrating every file from 10 hosts in 8 minutes generating 408,055 share access events.
DC SMB 445 collection: 06:52:37 to 07:00:48 UTC (8 minutes, 10 hosts, 408,055 share access events)
Internal targets accessed by both instances:
Domain controller, file server, backup server, 7 workstationsCloudflare Exfiltration
Both instances transmitted data over 443 to infrastructure sitting behind Cloudflare. The tool connected to over 6,900 unique IPs across both hosts all within Cloudflare ranges (104.x.x.x, 172.6x.x.x) not relying on a single IP for exfiltration. The volume of unique IPs suggests the exfiltration infrastructure is distributed across a large number of Cloudflare backed endpoints. The outbound connections continued until the threat actor was evicted from the network.
Domain Controller:
3,506 unique external IPs over 443
3,548 total outbound HTTPS connections
Backup Server:
3,460 unique external IPs over 443
3,456 total outbound HTTPS connections
Combined: 6,900+ unique Cloudflare IPs across both hosts (104.x.x.x, 172.6x.x.x)
Both hosts contributed roughly equal exfiltration volume.
Both continued outbound connections until eviction.Extortion
The threat actor did not drop a generic extortion note across the network. Each WARNING_DATA_LEAK.txt was written and addressed by name to the user of that specific workstation. The threat actor spent 68 minutes from 07:49 to 08:57 UTC placing the files in the Desktop, Downloads, and Documents folders on each host. The threat actor used a combination of RDP and SoftPerfect Network Scanner to deploy the notes. NetScan which was deployed on Day 1 and still running on the entry workstation was used to access remote SMB shares across the network while RDP was used to connect directly to hosts and place files manually.
The threat actor addressed leadership by their full names. They addressed regular employees by their first names only and included a line instructing them to pass the message to management. The threat actor was observed browsing Active Directory on the domain controller inspecting user accounts, group memberships, and job titles to identify who was leadership and who was regular staff.
Management Template
Dear [Admin Full Name], [Owner Full Name],
We hope this message finds you well. We are writing to inform you of a serious matter concerning your company’s data security. Our team has obtained a copy of your data, which is currently in our possession.
Think about the future of your business.
- Download and run Tor Browser from hxxps://www[.]torproject[.]org/download/
- Navigate to: [.onion negotiation portal - defanged]
- Log in using credentials: [unique login / password]
Sincerely, World Leaks
Employee Template
Dear [First Name],
Please pass this message on to your management.
[Same body text as management template] [Same Tor portal + credentials]
Sincerely, World Leaks
Extortion Infrastructure:
Group: World Leaks
Portal: vw6vklsuotptwdbiwqfvd7y4b57wdbfm6ypxduzzgbt62snti6jm76yd[.]onion
Leak Site: worldleaksartrjm3c6vasllvgacbi5u3mgzkluehrzhk2jz4taufuid[.]onionNegotiation
The threat actor directed the victim to a Tor negotiation portal using credentials provided in the extortion notes. The portal included a live chat interface where the threat actor communicated directly with the victim. The following is the full negotiation chat:
Timeline
| Time (UTC) | Event | Detail |
|---|---|---|
| Day before, 05:53 | RDP probe | 2 SYN packets from 45.227.254[.]128 |
| Day 1, 11:05 | First failed logon | Event 4625, Administrator, 2,153 attempts |
| Day 1, 11:07 | Brute force succeeds | Administrator’s password guessed correctly |
| Day 1, 11:11 | RDP logon | Administrator from 45.227.254[.]128 |
| Day 1, 11:13 | privacy.sexy | 110 commands on entry workstation |
| Day 1, 11:17 | NetScan deployed | Licensed copy with pre built config |
| Day 1, 11:26 | Cobalt Strike stager | PowerShell in process memory, C2 45.227.253[.]139:31822 |
| Day 1, 11:31 | lactenin.exe + C2 | Execution + first beacon to 195.66.213[.]218:4381 |
| Day 1, 11:31 | RDP to domain controller | Same brute forced Administrator account |
| Day 1, 11:32 | privacy.sexy on DC | TrustedInstaller escalation |
| Day 1, 11:38 | lactenin.exe to DC | SMB copy + immediate execution |
| Day 1 | Threat actor kicked out | Threat actor removed from network |
| Day 2, 05:57 | RDP back in | Administrator from 45.227.254[.]128 to entry workstation |
| Day 2, 05:59 | RDP to backup server | Administrator, first host accessed on Day 2 |
| Day 2, 05:59 | Veeam console opened | Browsed backup jobs, checked for virtualized infrastructure |
| Day 2, 06:06 | Ping infrastructure | 45.227.254[.]128 + 45.227.253[.]139 from backup server |
| Day 2, 06:24 | RDP reconnect to DC | Type 7 reconnect, Day 1 session still active |
| Day 2, 06:42 | SSH attempts (failed) | lactenin.exe to file server, 4 attempts |
| Day 2, 06:45 | agent.zip downloaded | Chrome on DC, source: temp[.]sh |
| Day 2, 06:47 | agent.exe dropped on DC | C:\ProgramData\Veeam\ |
| Day 2, 06:48 | agent.exe executed on DC | NORMAL mode, stdin config |
| Day 2, 06:49 | DC exfil begins | First HTTPS 443 to Cloudflare |
| Day 2, 06:52 | DC SMB sweep | 10 hosts over 445 in 8 minutes |
| Day 2, 06:55 | agent.exe to backup server | SMB copy to legitimate Veeam path |
| Day 2, 06:56 | agent.exe executed on backup | Second instance, NORMAL mode |
| Day 2, 06:57 | Backup exfil begins | 3,456 HTTPS connections, 3,460 unique IPs |
| Day 2, 07:49 | Extortion notes begin | Backup server via SMB C$ |
| Day 2, 07:49-08:18 | Notes on workstations | 7 workstations, name by name |
| Day 2, 08:57 | Final note on DC | Domain admin desktop |
| Day 2, continued | HTTPS exfil | 6,900+ Cloudflare IPs until eviction |
Indicators
Hashes
| File | SHA256 | Notes |
|---|---|---|
| lactenin.exe | a80f5c877ccc7fa71b9de1eb9bd82f9525f1ab282d15c4b4beaffabbf3064c31 | Go, masquerading as Edge Update |
| agent.exe | 743f9dbb32f86322c5f55f1e9051c5cd88092f10adcdac45aa648ac06e229b8a | Rust, RustyRocket exfil tool |
IPs
| IP | Port | Role |
|---|---|---|
| 45.227.254[.]128 | 3389 | External RDP source, SBSSRV |
| 195.66.213[.]218 | 4381 | lactenin.exe C2 |
| 45.227.253[.]139 | 31822 | Cobalt Strike HTTP beacon, URI /8qiJ |
Domains
| Domain | Role |
|---|---|
| temp[.]sh | Tool hosting (lactenin.zip + agent.zip) |
| vw6vklsuotptwdbiwqfvd7y4b57wdbfm6ypxduzzgbt62snti6jm76yd[.]onion | Negotiation portal |
| worldleaksartrjm3c6vasllvgacbi5u3mgzkluehrzhk2jz4taufuid[.]onion | Leak site |
MITRE ATT&CK
| Tactic | Technique | Detail |
|---|---|---|
| Initial Access | T1078 Valid Accounts | Administrator RDP brute forced from 45.227.254[.]128 |
| Defense Evasion | T1562.001 Impair Defenses | privacy.sexy, 110 commands, TrustedInstaller |
| Defense Evasion | T1036.005 Masquerading | Edge Update installer + Veeam directory |
| Credential Access | T1552.001 Credentials In Files | Harvested domain accounts |
| Lateral Movement | T1021.001 RDP | Entry workstation to DC and workstations |
| Lateral Movement | T1021.004 SSH | lactenin.exe to file server (failed) |
| Lateral Movement | T1021.002 SMB/Admin Shares | Tool distribution + C$ access |
| Command and Control | T1071.001 Web Protocols | lactenin.exe 195.66.213[.]218:4381 + CS 45.227.253[.]139:31822 |
| Command and Control | T1059.001 PowerShell | Cobalt Strike stager in process memory |
| Exfiltration | T1567 Exfiltration Over Web Service | 6,900+ Cloudflare IPs over 443 |
| Exfiltration | T1039 Data from Network Shares | agent.exe SMB 445 sweep of all hosts |
| Impact | T1486 Data for Impact | Personalized extortion notes per user |
References
- T. Ryan Whelan (Accenture), Rusty Rocket Overview - https://www.linkedin.com/posts/t-ryan-whelan-1156ab5_rusty-rocket-overview-activity-7427362471729995776-wgmI
- Microsoft Security Blog, Octo Tempest crosses boundaries to facilitate extortion, encryption, and destruction, October 2023 - https://www.microsoft.com/en-us/security/blog/2023/10/25/octo-tempest-crosses-boundaries-to-facilitate-extortion-encryption-and-destruction/